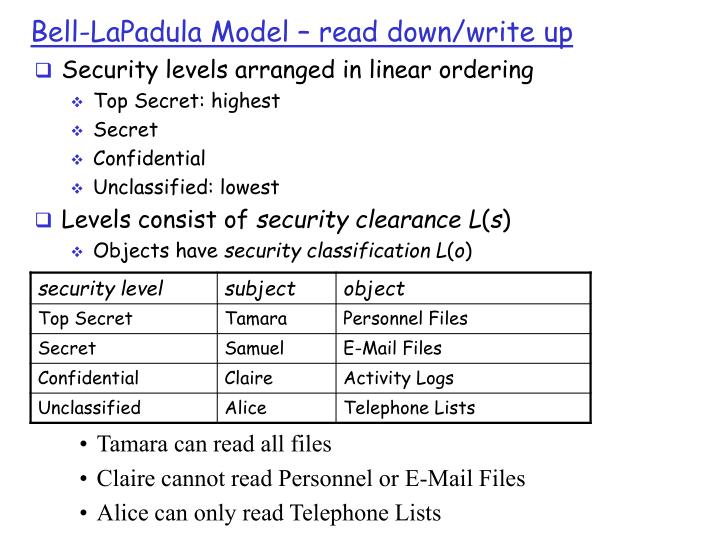
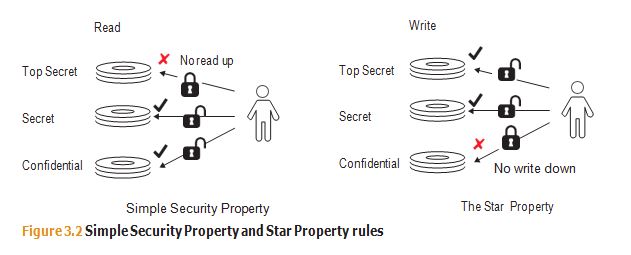
Bell-LaPadula Model Overview & Function | What is Bell-LaPadula Model? - Video & Lesson Transcript | Study.com

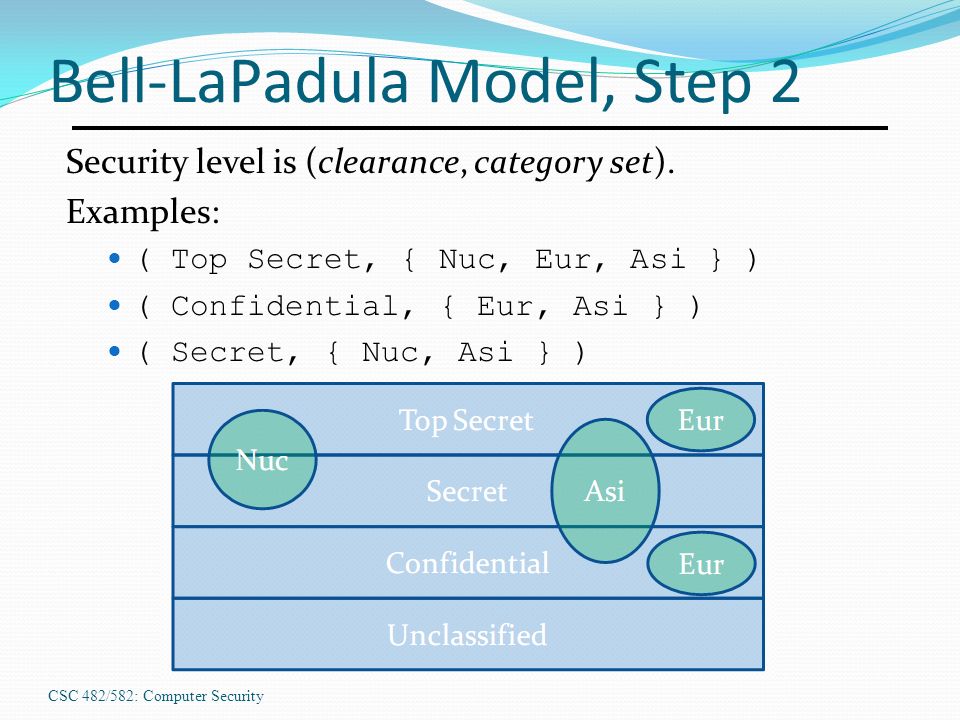
Bell Lapadula Confidentiality Model Ppt Powerpoint Presentation Gallery Graphics Cpb | Presentation Graphics | Presentation PowerPoint Example | Slide Templates
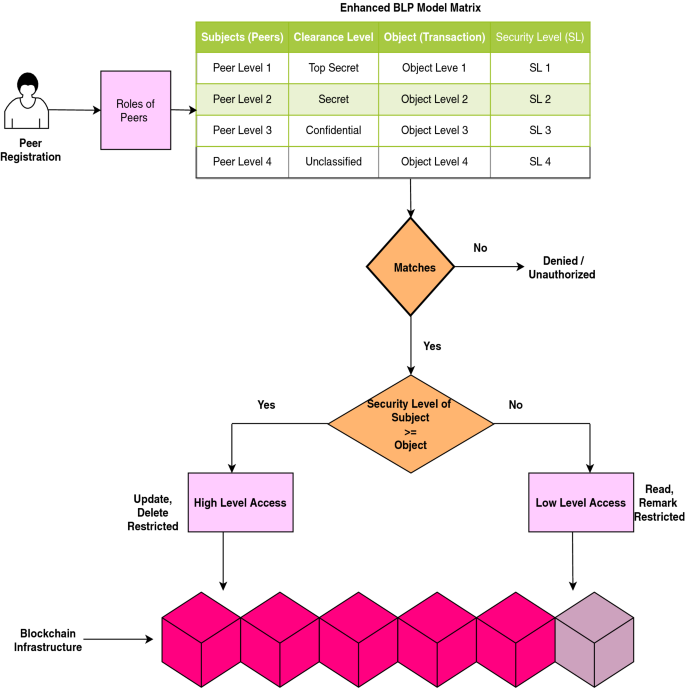
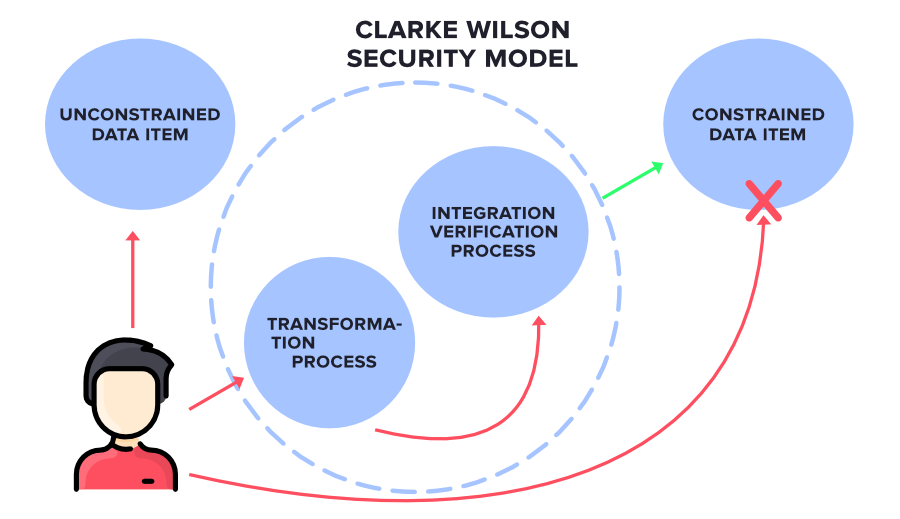
Scalable and secure access control policy for healthcare system using blockchain and enhanced Bell–LaPadula model | SpringerLink